by IntegriCom | Sep 25, 2025 | Cybersecurity, Uncategorized
A secure payment environment is critical for protecting customer data and sustaining trust in today’s digital economy. Businesses that handle credit card transactions must follow strict security protocols to prevent breaches and meet regulatory requirements. Adopting...

by IntegriCom | Aug 27, 2025 | Cybersecurity
Seamlessly moving business operations to the cloud requires careful planning, the right tools, and experienced guidance. Many organizations face challenges such as downtime risks, data security concerns, and integration complexities during this transition. Leveraging...

by IntegriCom | Aug 21, 2025 | Cybersecurity
Effective communication is the backbone of any successful business, influencing customer satisfaction, team efficiency, and overall performance. Modern technology now allows companies to connect their communication tools seamlessly, creating faster and more efficient...

by IntegriCom | Aug 18, 2025 | Cybersecurity
Technology plays a critical role in keeping businesses running smoothly, but the way companies manage their IT needs can vary greatly. Some rely on ongoing, proactive partnerships, while others seek help only when problems arise. These different approaches can impact...
by IntegriCom | Aug 11, 2025 | Cybersecurity
Cybersecurity threats are evolving rapidly, making it critical for businesses to implement strong, proactive defenses. A well-structured security framework doesn’t rely on a single tool; it layers multiple protection measures to address threats from different angles....
by IntegriCom | Jul 15, 2025 | Cybersecurity
To create a cybersecurity incident response plan, you need a clear roadmap to handle threats quickly and effectively. This post offers a step-by-step approach on how to create a cybersecurity incident response plan, covering everything from preparation to recovery....
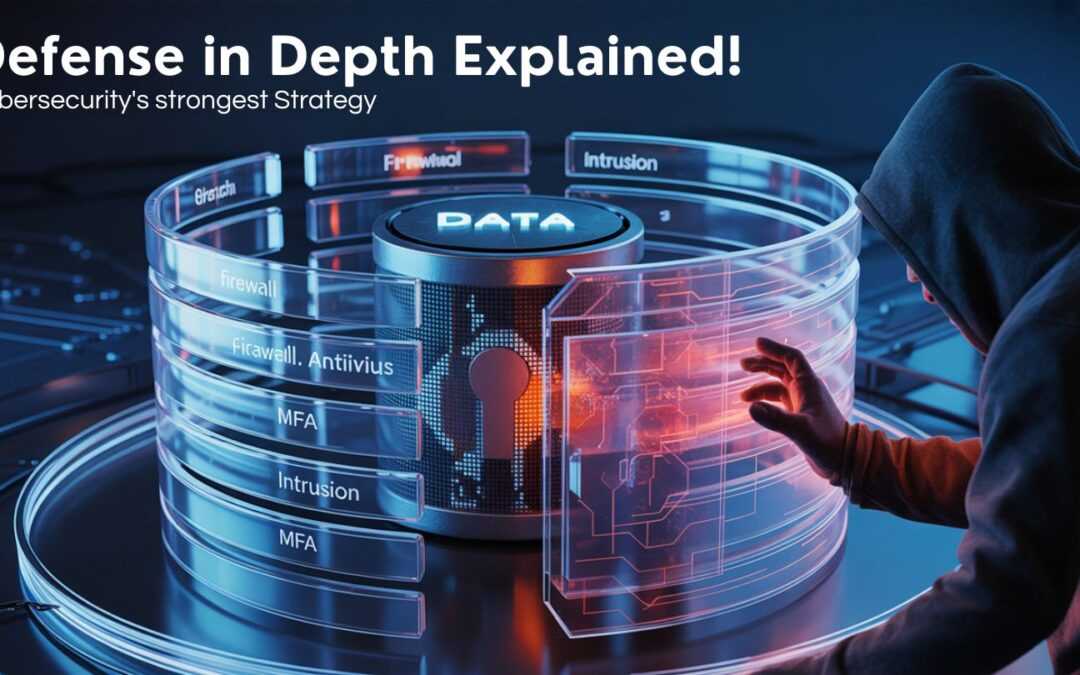
by IntegriCom | Jun 12, 2025 | Cybersecurity
Defense in Depth (DiD) in cybersecurity is a strategy that uses multiple layers of security to protect against breaches. It doesn’t rely on just one defense but combines different measures to keep threats at bay. This blog will show you what defense in depth is in...

by IntegriCom | Jun 5, 2025 | Cybersecurity
Managed IT services are vital in remote working environments, offering key tools, strong cybersecurity, and 24/7 support. As remote work grows, the role of managed IT services in remote working environments helps businesses remain productive and secure. In this post,...

by IntegriCom | May 15, 2025 | Cybersecurity
Phishing is one of the most common and dangerous cybersecurity threats out there, targeting both individuals and businesses alike. But don’t worry! This blog will walk you through the types of phishing attacks and how you can stop them effectively. From email scams to...

by IntegriCom | May 2, 2025 | Cybersecurity
Cybersecurity and cyber resilience are both essential for protecting your digital world, but they’re not the same. Cybersecurity is all about stopping attacks before they happen, while cyber resilience focuses on bouncing back quickly and keeping things running...
by IntegriCom | Apr 30, 2025 | Cybersecurity
As cyberattacks continue to surge in both frequency and sophistication, cyber insurance has become a vital part of a company’s risk management strategy. Once considered “nice-to-have,” cyber coverage is now essential for businesses of all sizes — especially small to...

by IntegriCom | Apr 21, 2025 | Cybersecurity, Uncategorized
Cybersecurity threats compromise systems and steal data. Knowing the most common threats is essential to safeguard information and ensure business continuity. This blog highlights key cybersecurity threats and the importance of a professionally managed defense...